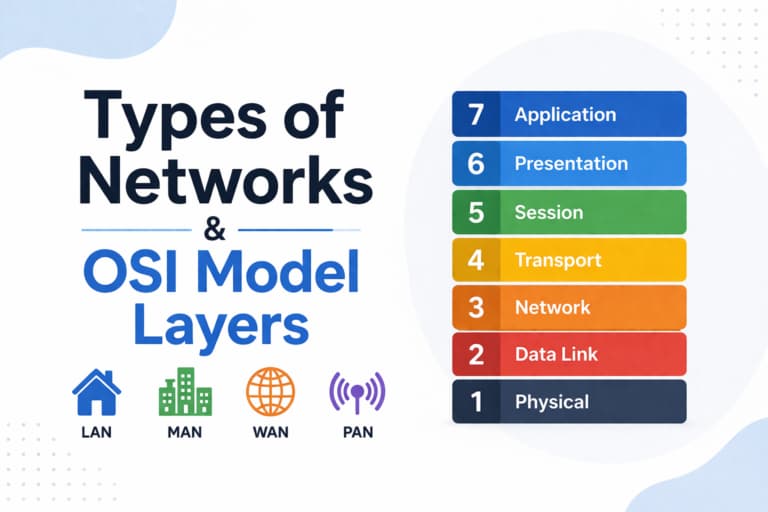
This guide covers both types of networks and OSI model layers with a reference table and examples.
Types of Networks
- PAN (Personal Area Network)
- LAN (Local Area Network)
- WAN (Wide Area Network)
- MAN (Metropolitan Area Network)
Networks can be divided into two main types based on how devices communicate and share resources.
Peer-to-Peer Network
A peer-to-peer (P2P) network is a type of network where all computers are equal and can share resources directly without a central server.
In this model, each device can act both as a client and a server.
Advantages of Peer-to-Peer Networks:
- Easy to set up and maintain
- Low cost (no dedicated server required)
- Direct resource sharing between devices
Disadvantages:
- Limited scalability
- Lower security
- Difficult to manage in larger environments
Client-Server Network
A client-server network is a model where a central server provides resources and services to multiple client devices.
The server manages data, applications, and security, while clients request access to these resources.
Advantages of Client-Server Networks:
- Centralized management
- Better security and control
- Scalable for large environments
Disadvantages:
Requires maintenance and administration
Higher cost (server required)
OSI Model Overview
The OSI model (Open Systems Interconnection) is a conceptual framework used to understand how data is transmitted across a network.
It was developed by the International Organization for Standardization (ISO) and defines seven layers that describe how different networking systems communicate.
Each layer has a specific role and works together with the other layers to ensure reliable data transmission.
The OSI model helps engineers, system administrators, and network professionals design, troubleshoot, and understand network communication in a structured way.
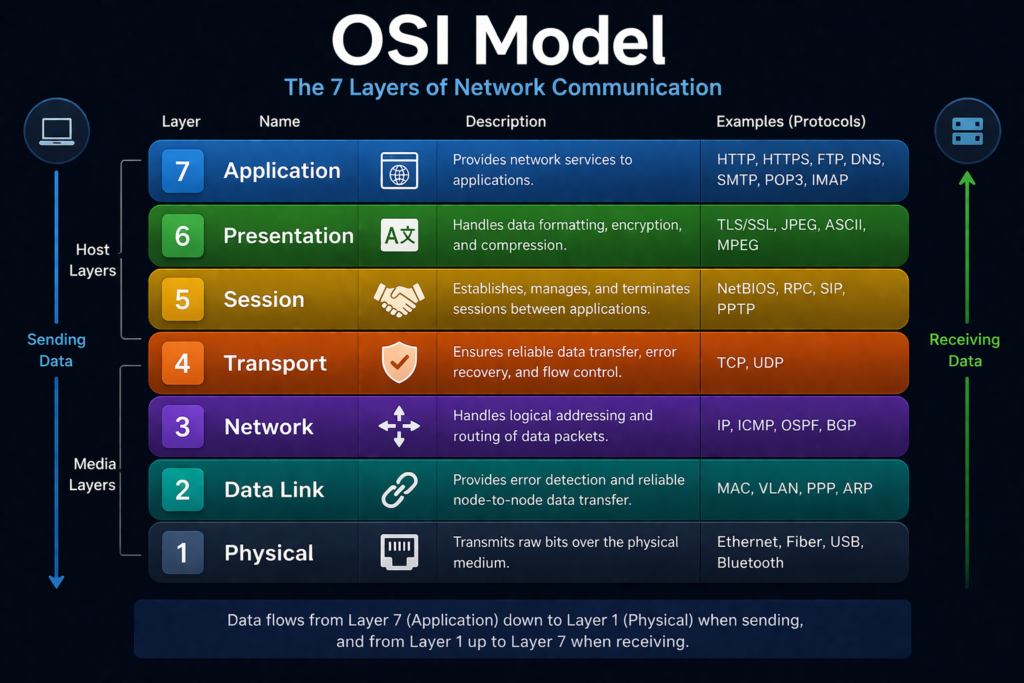
OSI Model Layers Reference Table
| Layer # | Layer Name | PDU | Responsibility | Common Protocols |
| 7 | Application | Data | Network services to user applications | HHTTP, FTP, SMTP, DNS |
| 6 | Presentation | Data | Data formatting, encryption, compressio | SSL/TLS, JPEG, GIF |
| 5 | Session | Data | Session management between systems | NetBIOS, RPC |
| 4 | Transport | Segments (TCP) / Datagrams (UDP) | End-to-end communication | TCP, UDP |
| 3 | Network | Packets | Routing and logical addressing | IP, ICMP, IPSe |
| 2 | Data Link | Frames | MAC addressing and error detection | Ethernet, Switch |
| 1 | Physical | Bits | Transmission of raw binary data | Fiber, Hubs, Repeaters |
The table above summarizes all OSI layers, their responsibilities, and commonly used protocols. This reference helps quickly understand how data flows through different layers in a network.
OSI Model Layers Diagram
OSI Model Layers Explained in Detail
7. Application Layer
The Application layer is the closest layer to the end user and provides network services directly to applications such as web browsers, email clients, and file transfer tools.
This layer enables user interaction with the network and supports services like web browsing, email communication, and file transfers.
Common protocols include HTTP, HTTPS, FTP, SMTP, DNS, POP3, and IMAP.
6. Presentation Layer
The Presentation layer is responsible for formatting, encrypting, and compressing data before it is transmitted.
It ensures that data sent from one system can be properly read by another, regardless of differences in data representation.
This layer also handles encryption technologies such as SSL/TLS and supports formats like JPEG, GIF, ASCII, and MPEG.
5. Session Layer
The Session layer manages communication sessions between applications.
It is responsible for establishing, maintaining, and terminating connections between systems. It also ensures that data exchange happens in an organized and synchronized way.
Protocols and services include NetBIOS, RPC, and session control mechanisms.
4. Transport Layer
The Transport layer ensures reliable data delivery between devices.
It breaks data into segments, manages error detection and correction, and controls data flow to prevent congestion.
Two key protocols operate at this layer:
- TCP (Transmission Control Protocol) – reliable and connection-oriented
- UDP (User Datagram Protocol) – faster but less reliable
3. Network Layer
The Network layer is responsible for routing and logical addressing.
It determines the best path for data to travel across networks and ensures packets reach the correct destination.
Key protocols include IP, ICMP, OSPF, and BGP.
Devices operating at this layer include routers and Layer 3 switches.
2. Data Link Layer
The Data Link layer ensures reliable data transfer between directly connected devices.
It handles framing, MAC addressing, and error detection.
This layer is divided into two sublayers:
- MAC (Media Access Control)
- LLC (Logical Link Control)
It also manages how devices access the physical medium and prevents data collisions.
1. Physical Layer
The Physical layer is responsible for transmitting raw binary data over a physical medium.
It deals with hardware components such as cables, connectors, and electrical signals.
Examples include Ethernet cables, fiber optics, radio signals, and network hardware like hubs and repeaters.
Understanding the OSI model layers is essential for working with modern networks, servers, and cloud infrastructure.